Learn Technology What you really want
The future is closer than you think. You can pay attention now or watch the transformation happen right in front of your eyes.
Close or press Esc
The future is closer than you think. You can pay attention now or watch the transformation happen right in front of your eyes.



Learn AWS security from Expert. Book for Demo Session



Learn AWS SysOps Administrator from experts. Book now for free demo session



Learn AWS Solution Architect from Experts. Book now for free demo session



AWS DevOps Training and Placement in Chennai with Both Classroom and Online.



Best Social Medial Marketing course from Marketing expert. Enroll now for Free Demo Session.



Best Content Writing training from expert. Book now for Free Demo Session



Best SEO Training in Chennai from Industry Expert. Book for Free Demo Session now.



Best Digital Marketing Course in Chennai from Industry Experts. Book for Free Demo Session now.



Learn SQL from industry experts. Book for free demo session



Real Time MongoDB Training from Certified Experts. Book for free demo session now.



Learn Teradata Course from Top Class Talents. Book for free demo session now.



Real Time Oracle DBA Training from experienced DB Professionals. Call us for free demo session now.



BITA Academy provides the best Ruby on Rails training in Chennai
Learn UI UX Design from experts in 3 months
Learn PHP from Experts. Book For Free Demo Session



Hands on JavaScript Training from Industry Experts. Call for free demo session now.
Best Hands on Training in ReactJs from Industry Experts. Call us for free demo now.



Best Spring Training by industry experts to gain deep knowledge in advanced java.



Hands on Node.js Training in best price. Enroll now for free demo session.
Best Real Time Hibernate Training from Industry Experts



Web Design Training Course for Beginners and Experienced from Top Class Experts



Mean Stack Course for Corporate Professionals. Enroll for free demo Class now



Angular course with hands-on training session. Call us if you need free demo session.
Real Time Flutter Dart Training in Chennai from industry experts. Enroll now for free demo session.
Learn iOS Training in Chennai at BITA Academy and become a certified iOS Developer.



Learn Android Course from Industry Experts and become an Android Developer.



Learn from experts. Enroll now for free demo session.



Learn Ethical Hacking Course from Top Class Experts.



Best Cloud Security Course in Chennai for IT Professionals



Real Time Hands on SAP ABAP Training from industry experts



Real Time Hands on SAP FICO Training from Industry Experts
Learn Tableau From Experts. Book for Free Demo Session



Learn Power BI Tool From Expert. Book For Free Demo Session



Want to know more about PySpark.Lets hear what Industry Experts Say.
Learn Informatica Course to know more about data integration products.



Want to know what Blockchain is about? Enroll now for free demo session.
Do you want to learn Hadoop and its components. Enroll for free demo session now.
Want to Analyse,Process and Extract information from Complex Data Sets. Enroll for Big Data Course now
BITA provides C C++ Training in Chennai for college students and freshers.



Core Java Training Course in Chennai



Want to become a Full Stack Developer. Call us for a free demo session with our Industry Experts.



Java is most popular for Android smartphone apps. Get the Best Java Developer Course from us.



Advanced Open Source framework for mobile and web development. Register now for free demo session.
Python Scripting Course for Beginners from Industry Experts. Best Offers for College Students.
Learn J2EE if you want to gain deep knowledge in advanced java. Register now.



Hands on Penetration Testing Training. Book for Free Demo Session



Learn Playwright Automation to upgrade yourself. Book For Free Demo Session



Learn Katalon Studio from Experts. Book for free demo session



Learn Tosca Automation from professionals. Book for free demo session



Learn ReadyAPI training from expert. Book for free demo session



Real Time Hands on Security Testing Training from our industry experts. Enroll now for free demo session.



Portable framework for testing web applications. Register now to learn more about Test Automation.



Learn JMeter Course and know more about performance test for web apps. Register now.
Real Time Hands on QTP Training from industry experts. Enroll for free demo session now.



Hands on Load Runner Training to analyse the key components of the application. Enroll now.



Want to execute test cases manually with out any automations tools. Register for Manual Testing Course now.



Open Source Test Automation framework for hybrid and mobile web apps. Enroll now.



Automated UI Testing Tool to create and execute functional test. Enroll now to learn more.
Get started with Real Time REST API Testing Training course from our industry experts. Register now.



End to End Test Framework for Angular applications. Register now to hear more from our experts.
Learn from expert. Book for free demo session.
Learn from experts. Book for free demo session



Real Time Microstrategy Training for Professionals who wants to be an BI expert. Enroll for free demo session now.
Hands On Ab Initio Training from Industry Experts. Enroll now for free demo session.



Real Time Cognos Training from Industry Experts. Call us for free demo session.
Real Time AI Training from Industry Experts. Call us now for a free demo session
Real Time Data Science Training in Chennai from Industry Experts. Enroll now for free demo session.



Machine Learning focus on statistics and algorithms that is essential for AI apps. Enroll now.



Learn Data Science with R Programming from Industry Experts. Register now.
Real Time UiPath Training from Industry Experts. Enroll now for free demo session.
Learn Automation Anywhere and get deep knowledge about software bots. Call us for free demo session now.



Hands on Blue Prism Training from Industry Experts. Enroll for free demo session now.
RPA Technology derives business process automation based on artificial intelligence. Enroll now.



Master Mulesoft from Professionals. Book For Free Demo Session
Master Openshift from Expert. Book for Free Demo Session



Learn Azure Solution Architect from expert. Book now for free demo session



Learn Azure Administrator from Experts. Book for free demo session



Learn Microsoft Azure Developer Training from Experts. Book for Free Demo Session



Learn Azure Security from expert. Book for Free Demo Session



Best VMware Training Fom Expert. Book For Free Demo Session



Best Salesforce Analytic Training from Leading Analytics. Book now for Free Demo Session



Best Salesforce Admin Certification Training from Industry Expert. Book now for Free Demo Session



Best Salesforce Developer Training from Real time Developers. Book now for Free Demo Session



Hands on GCP Training from Cloud Expert. Book now for Free Demo Session



Hands On OpenStack Training in Chennai from experienced Professionals. Book a slot for a free demo session now.



Real Time Salesforce Developer Training from Industry Experts. Enroll now for free demo session.
Learn from experts. Book now for free demo session



Learn from experts. Enroll now for free demo session
Learn from experts. Enroll now for demo session



Learn from expert. Book for free demo session



Learn Excel From Expert. Book for Free Demo Session



Join kids program and cultivate your creativity



Best Workday Training in Chennai from Industry Experts. Call now for free demo session.
Real Time Docker Training from Industry Expert. Book now for free demo session.



Learn more about open source UNIX like OS from Industry experts. Register now.
Learn PERL to perform web development and system administration. Register now.
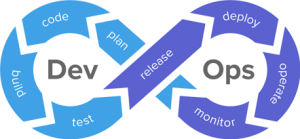
Let's hear what Industry Experts talk about DevOps Culture. Register now.



Vedic Maths Course for School Students and Kids to learn Maths in Simple ways. Register now



Placement Training for College Students and Freshers from Corporate Trainers. Enroll now.
Learn IoT Technology real time from experienced professionals. Register now for demo session.
Security testing is one of the most important types of testing and its objective is to find bugs or vulnerabilities of the software or any computer or web-based application. It is being done to shield the records from an unexpected attack or intruder.
Many applications contain confidential data that can also require protection. It need to be finished periodically in order to identify the threats so that an immediately motion can be taken if an attack is being done.
The Vulnerability can be described as weak spot of any machine through which intruders or bugs can attack on the system.
If security testing has not been carried out carefully on the gadget then probabilities of vulnerabilities get increase. Time to time patches or fixes requires stopping a machine from the vulnerabilities.
Intrusion detection system basically detects the possibility of an attack,It collects the data from a number of sources, analyzes the data and finds out all possible ways to attack the system. It checks for the following:
A fault in a software which motives the software to operate in an unintended or unanticipated manner.
Following attributes are considered for security testing:
There are four main focus areas to be considered in security testing (Especially for web sites/applications):
• Network security: This involves looking for vulnerabilities in the network infrastructure (resources and policies).
• System software security: This involves assessing weaknesses in the various software (operating system, database system, and other software) the application depends on.
• Client-side application security: This deals with ensuring that the client (browser or any such tool) cannot be manipulated.
• Server-side application security: This involves making sure that the server code and its technologies are robust enough to fend off any intrusion.
Penetration testing is on the security testing which helps in identify vulnerabilities in a system.Penetration test is an attempt to evaluate the security of a system by manual or automated techniques and if any vulnerability found, testers uses that vulnerability to get deeper access to the system and find more vulnerabilities.
The main purpose of this testing to prevent a system from any possible attacks.
Penetration testing can be done by two ways .
In white box testing, all the information is available with the testers whereas in black box testing, testers don’t have any information and they test the system in real world scenario to find out the vulnerabilities.
Linux has some commands that Windows does not, but Windows is no longer open supply and does now not suffer from current hacks such as Heartbleed.
Two common techniques to protect a password file are- hashed passwords and a salt value or password file access control.
Due to following reasons Penetration testing must be used by the testers:
Abbreviations related to software security are:
You can use PGP to encrypt email messages or some other form of a public private key pair system where only the sender and the recipient can read the messages.
ISO/IEC 17799 is at the start posted in UK and defines excellent practices for Information Security Management. It has guidelines for all organizations small or big for Information security.
Testing can be of following types:
The seven main types of security testing as per Open Source Security Testing methodology manual are:
SOAP – Simple Object Access Protocol that is an XML based protocol that is used to exchange information over HTTP. Web services sent XML request in SOAP format and then SOAP client sends a message to the server. The server then responds back with a SOAP message.
WSDL or Web Services Description Language is an XML formatted language that is used by UDDI. It describes the web services and the way in which they can be used and accessed.
The parameters that define an SSL session connection are:
This variety of attack makes use of the forceful looking with the URL manipulation attack. Hackers can manipulate the parameters in url string and can get the critical data which generally no longer open for public such as executed data, historic version or data which is under improvement
There are three benefits of an intrusion detection system.
HIDS or Host Intrusion Detection system is a system in which snapshot of the existing system is taken and compares with the previous snap shot. It checks if critical files were modified or deleted, then an alert is generated and sent to the administrator.
Following are the participants:
URL manipulation is a kind of attack in which hackers manipulate the website URL to
get the fundamental information. The data is exceeded in the parameters in
the query string by means of HTTP GET method between client and server. Hackers can
alter the information between these parameters and get the authentication on
the servers and steal the critical data.
In order to avoid this sort of attacks security testing of URL manipulation need to be done. Testers themselves can try to manipulate the URL and check for possible attacks and if discovered they can prevent these types of attacks.
Following are the three classes of intruders:
Secure Sockets Layer protocol or SSL is used to make secure connection between client and computers.
Below are the component used in SSL:
Ports are the point from where information goes in and out of any system. Scanning of the ports to find out any loop holes in the system are known as Port Scanning. There can be some weak points in the system to which hackers can attack and get the critical information. These points should be identified and prevented from any misuse.
Following are the types of port scans:
Cookie is a piece of information received from web server and stored in a web browser which can be read anytime later. Cookie can contain password information, some auto fill information and if any hackers get these details it can be dangerous.
Types of Cookies are:
The parameters that define an SSL session state are:
The time investment for a penetration test varies from case to case depending on the systems to be tested and the individual test requirements. Usually, the time needed ranges from a few days to several weeks. One goal of the preliminary meeting is to get enough information about the systems to be tested to estimate the optimal length for the penetration test.
Human resources on the customer’s side are usually only marginally bound. Most notably, a contact person for questions during the exploitation phase is required.
The type and amount of information needed varies with the kind of penetration test that is to be conducted. The two concepts mentioned most often are blackbox and whitebox tests. Unfortunately, those terms are not defined by a standard and can therefore mean different things, depending on who you talk to.
Red Team Penetration Testing usually recommends a whitebox test. Penetration tests performed as complete blackbox tests always suffer from the fact that third parties might get involved without their explicit consent. Providing technical information in a whitebox test scenario before the test starts also allows the penetration testers to detect security vulnerabilities that are of importance to your company even faster and more efficiently.
It should always be acted on the assumption that real, serious attackers are able to obtain the necessary information prior to their attacks, or can procure it in time. A precise determination about what information is necessary to conduct an efficient test is done individually for every client during a preliminary meeting.
Denial-of-service (DoS) attacks are usually only examined if it seems to be possible to put a system’s availability at risk with very small effort. This can for example be a misconfiguration or a program error (say, if a system crashes when it gets sent an overly long request). Attacks like this will only be performed after an explicit agreement is provided, to verify if the attack is indeed possible.
On the other hand, attacks that try to saturate the bandwidth a company has at its disposal are usually not tested, as this is always possible for attackers with sufficient resources and will also affect third-party systems. Distributed denial-of-service attacks, that usually involve hundreds, if not thousands, of zombie systems (systems that were compromised and can now be remotely controlled) cannot be simulated realistically.
A penetration test, also referred to as “pentest”, is a method of evaluating the security of a computer system or network by using simulating an attack from malicious outsiders (without any authorized means of accessing the company’s networks) but also malicious insiders (who have some level of authorized access).
The technique involves an active analysis of the system for any potential vulnerabilities that could result from poor or improper system configuration, recognized and unknown hardware or software flaws, or operational weaknesses.
The analysis is carried out from the position of a achievable hacker and can involve active exploitation of security vulnerabilities.
If you have your own IT department implemented in your security system, it is to your advantage to let an impartial third party do the audit. We provide an outsiders view on how easy/difficult it is to compromise your integrity. Having an audit report from a third party, outlining all confirmed security vulnerabilities on the network provides invaluable information to any network administrator.
The service is fast, and you will have the advantage of continually knowing how secure your network is and what you can do to improve it.
Yes we can check any and as many IP addresses as your desires provided they belong to you. We will not test any third party IP address.



BITA – Best IT Academy is a leading IT training hub driven by IT professionals. We offer a competent platform to enable powerful and positive transformation in IT for better career opportunity and advancement.
No:1/37, Bharathiyar Street,
Moovarasampet Madipakkam,
Chennai 600 091.
Phone: +91 9176 00 4616
Nearby Locations: Ramapuram, DLF IT Park, Valasaravakkam, Adyar, Adambakkam, Anna Salai, Ambattur, Ashok Nagar, Aminjikarai, Anna Nagar, Besant Nagar, Chromepet, Choolaimedu, Guindy, Egmore, K.K. Nagar, Kodambakkam, Ekkattuthangal, Kilpauk, Medavakkam, Nandanam, Nungambakkam, Madipakkam, Teynampet, Nanganallur, Mylapore, Pallavaram, OMR, Porur, Pallikaranai, Saidapet, St.Thomas Mount, Perungudi, T.Nagar, Sholinganallur, Triplicane, Thoraipakkam, Tambaram, Vadapalani, Villivakkam, Thiruvanmiyur, West Mambalam, Velachery and Virugambakkam.
Copyrights © 2024 Bit Park Private Limited · Privacy Policy · All Rights Reserved · Made in BIT Park Pvt Ltd
